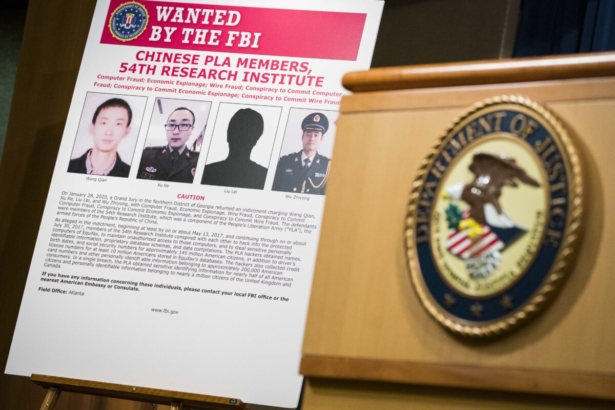
To access data from unsuspecting users, the Chinese Communist Party (CCP) could be exploiting a universal authentication process that's thought to be secure, but in reality may not be, cybersecurity experts have warned.
While encryption remains the preferred method to secure digital data and protect computers, in some cases, the very digital certificates used for authentication on the internet are allowing the Chinese regime to infiltrate various computer networks and wreak havoc, they said.
Bodies around the world, known as “certificate authorities” (CA), issue digital certificates that verify a digital entity’s identity on the internet.
A digital certificate can be compared to a passport or a driver’s license, according to Andrew Jenkinson, CEO of cybersecurity firm Cybersec Innovation Partners (CIP) and author of the book “Stuxnet to Sunburst: 20 Years of Digital Exploitation and Cyberwarfare."
“Without it, the person or device they are using cannot be according to industry standards, and vital data encryption could be bypassed, leaving what was assumed to be encrypted in plain text form,” Jenkinson told The Epoch Times.
Layers of False Trust
Michael Duren, executive vice president of cybersecurity firm Global Cyber Risk LLC, said that digital certificates are typically issued by trusted CAs, and equal levels of trust are then passed on to intermediate providers. However, there are opportunities for a communist entity, a bad actor, or another untrustworthy entity to issue certificates to other “nefarious folks” that would appear to be trustworthy but aren't, he said.“When a certificate is issued from a trusted entity, it’s going to be trusted," Duren said. "But what the issuer could actually be doing is passing that trust down to someone that shouldn’t be trusted.”
Duren said he would never trust a Chinese certificate authority for this reason, stating that he's aware of a number of companies that have banned Chinese certificates because they've been issued to entities that can't be trusted.
Jenkinson said that Chinese certificate authorities make up a small proportion of the overall sector, and the certificates they issue are typically confined to Chinese entities and products.
In 2015, certificates issued by the China Internet Network Information Center (CNNIC), the state-run agency that oversees China’s domain name registry, were called into question. Google and Mozilla banned CNNIC certificates upon learning of unauthorized digital certificates connected to several domains. Both internet firms objected to the CNNIC delegating its authority to issue certificates to an Egyptian company, which issued the unauthorized certificates.
According to Jenkinson, the CNNIC certificates were banned because “they had back doors in them.”
“A back door means [the Chinese certificate authority] could literally take over administration access and send data back to the mothership,” he said.
Security Flaw
Despite these bans on Chinese digital certificates in recent years, the CCP hasn't been deterred and is playing the long game, Jenkinson said.He pointed to an alarming discovery made by his cybersecurity firm two years ago, affecting a multinational consulting company.
Typically, digital certificates are valid for a couple of years, depending on the certification authority, and renewal is required to keep them valid and the data they're supposed to protect secure, he said.
“But in 2019, CIP Chinese discovered certificates that were in place for 999 years,” Jenkinson said.
His firm made this discovery when examining the laptops of a prominent global consulting company.
Jenkinson brought this security flaw to the firm’s attention and offered services to secure its computer and customer networks. But the company declined.
“Either they are incredibly complacent, or they are complicit,” he said, noting that the company’s clients include U.S. government entities.
This multi-billion-dollar company’s failure to remedy this issue means that hundreds of thousands of people could be exposed to Chinese infiltration via this firm’s lax security, Jenkinson said.
The firm is compromising its customers every time someone uses one of their laptops, he said. For example, companies or clients using the company’s services could be held to ransom, have their intellectual property stolen, or be the recipient of malicious codes planted for later use.
This company is “in breach of every regulation of privacy known to man—and they just want to dismiss it,” the cybersecurity professional said, particularly pointing to the EU’s strict data protection laws.
And if this information were made public, the repercussions would be extensive, Jenkinson said.
“Imagine a waterhole attack or a drive-by attack, one where a cybercriminal can just sit there and easily gain access to capture data without even thinking about it or having to decrypt it—because it’s all in plain text [due to a rogue certificate or configuration error],” he said.
A 'Slippery Slope'
Economic losses from cybercrimes are far from trending in the right direction, according to Jenkinson.Global losses from cybercrime exceeded $1 trillion in 2020, according to a report from computer security company McAfee. In 2021, losses are expected to escalate to more than $6 trillion, research firm Cybersecurity Ventures said.
Jenkinson predicts that economic losses will exceed $10 trillion by 2025.
“This will impact every man, woman, and child," he said. “The slippery slope we’re on, well, we’re greasing it ourselves.”
As a start to reversing this trend, “people should not be using CNNIC digital certificates,” Jenkinson said.
Duren of Global Cyber Risk agreed, saying, “Anything coming out of a state-controlled entity like communist China acting as a certificate authority should not be trusted.”
CAs need better controls and oversight, Jenkinson said. “Without this, nobody has any chance of knowing what digital certificates are being used, considering that a standard laptop contains hundreds of thousands of digital certificate instances.”
Jenkinson noted that Chinese computer products will predominately use Chinese digital certificates. Therefore, users of such products should be aware that their security could be compromised as a result.

